Penetration Testing That Protects Your Business
Comprehensive vulnerability assessment with expert-led security analysis and actionable remediation guidance.
Featured Security Assessments
Real-world penetration testing results from recent engagements
Penetration Testing Services
Expert security testing across all attack surfaces
Web Application
OWASP Top 10, business logic flaws, authentication & session management testing.
Mobile Application
iOS & Android security analysis including reverse engineering and data protection.
API Testing
REST, GraphQL & SOAP API security — authorization, rate limiting, data exposure.
Network Infrastructure
External & internal network assessments, firewall review, segmentation analysis.
Cloud Security
AWS, Azure & GCP infrastructure assessment — IAM, storage, compute configs.
Kubernetes
Cluster security testing — RBAC, pod security, network policies, container escape.
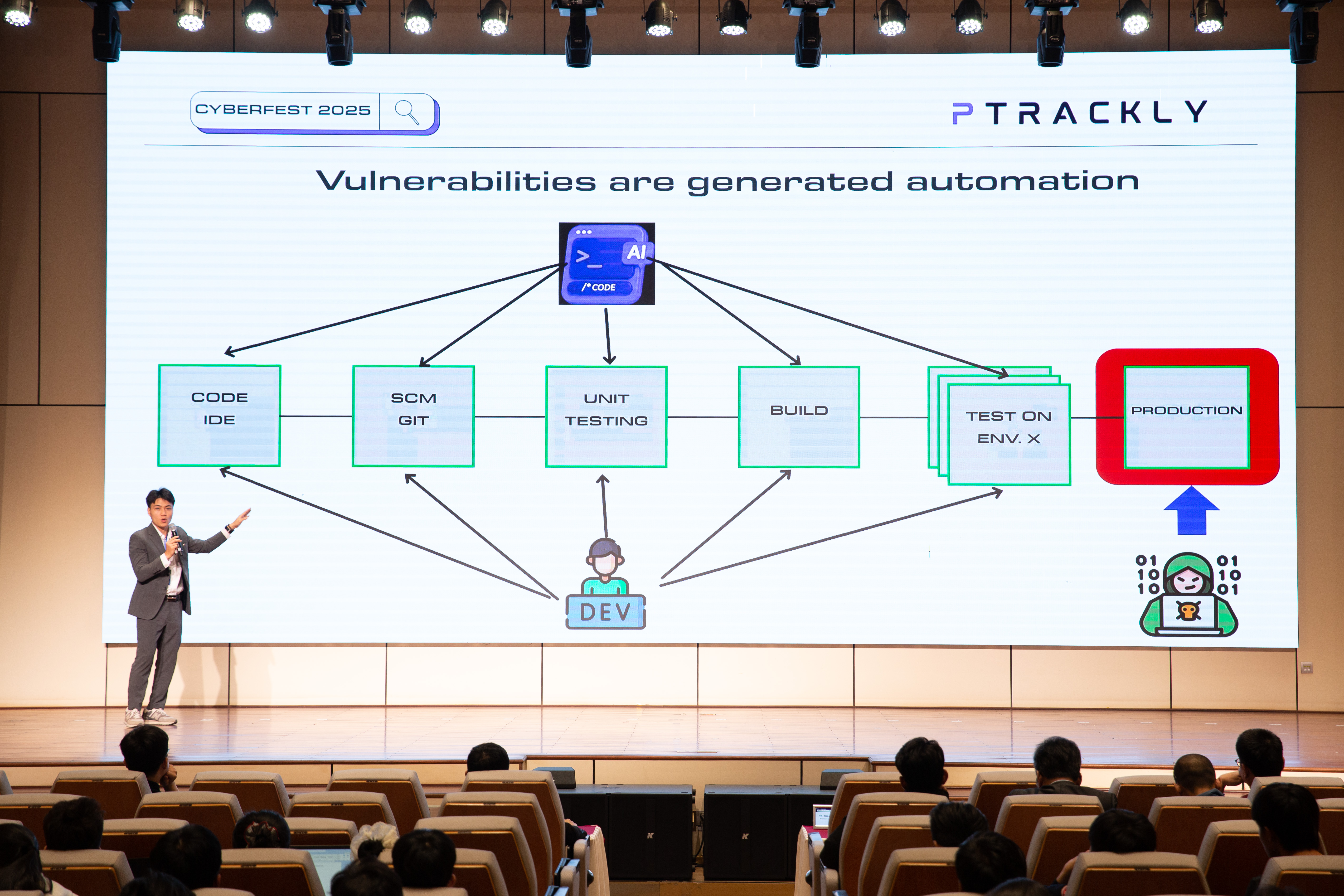
Our Methodology
A proven approach to identifying and validating security vulnerabilities
Reconnaissance
Attack surface mapping & intelligence gathering
Analysis
Automated scanning with manual verification
Exploitation
Validate exploitability of vulnerabilities
Reporting
Detailed reports with remediation guidance
Internationally Recognized Certifications
Our team holds the industry's most prestigious cybersecurity certifications
Community & Industry Contributions
Active participation in the global cybersecurity community
Bug Bounty Programs
Active participation in CyberFest, Hackathon, and private programs with top rankings
Open Source Security
Contributing security patches and tools to major open source projects
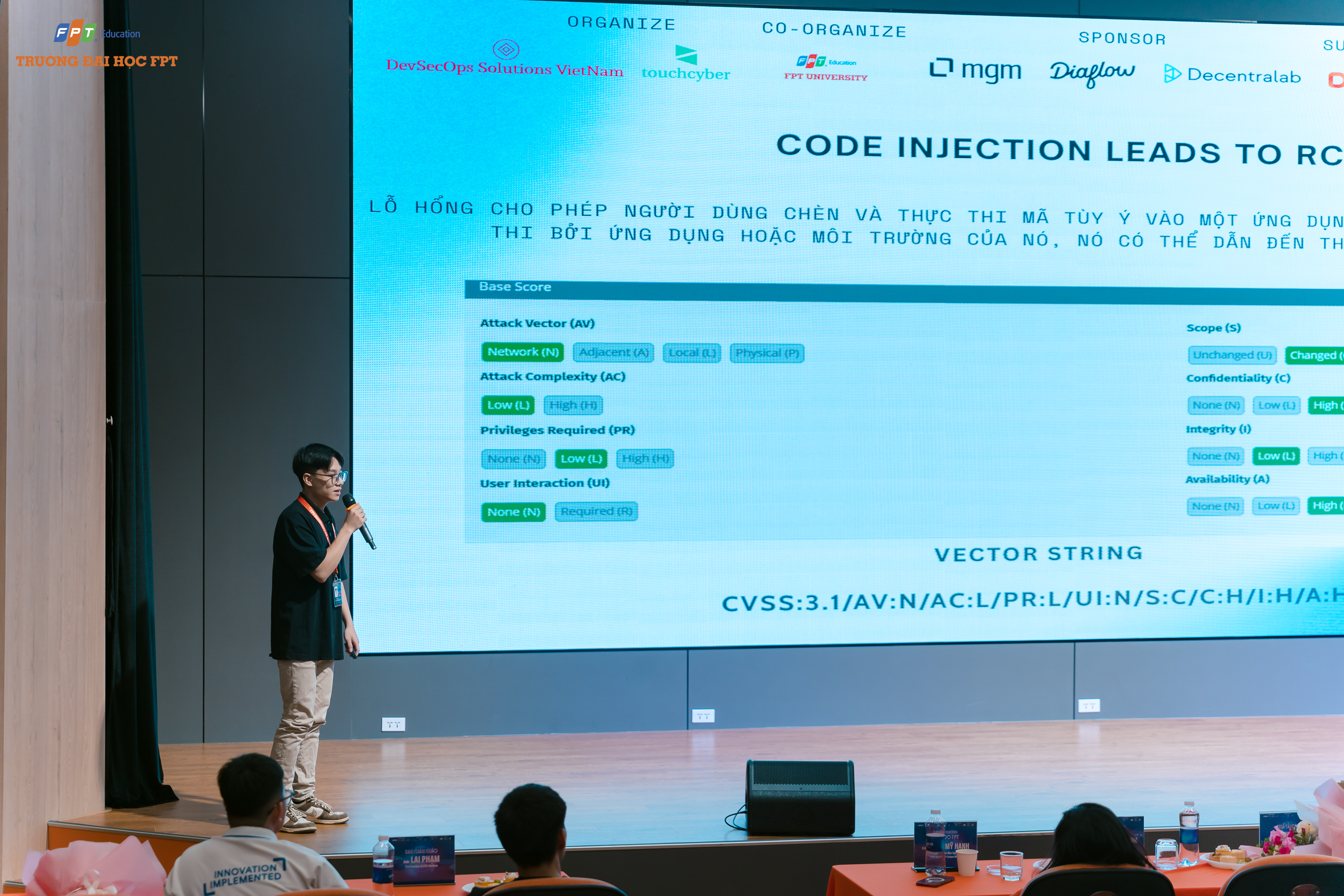
Conference Speaking
Regular speaker at CyberFest, DevSecOps, and regional security conferences
Security Research
Publishing original research on emerging threats and attack techniques
Training & Workshops
Conducting hands-on security training for enterprises and security professionals
Community Leadership
Leading local DevSecOps chapters and organizing security meetups across Asia-Pacific
Events & Workshops
Highlights from security conferences, training sessions, and community events






Frequently Asked Questions
Answers to common questions about penetration testing services
What does a penetration test include?
Our penetration testing service covers a comprehensive scope including web application testing (OWASP Top 10, business logic flaws), API security testing (REST, GraphQL, SOAP), cloud infrastructure assessment (AWS, Azure, GCP misconfigurations), and network penetration testing (external and internal). Each engagement includes reconnaissance, vulnerability identification, manual exploitation to validate findings, and a detailed report with prioritized remediation guidance.
How long does a pentest take?
A typical penetration test takes 1-2 weeks depending on scope and complexity. A focused web application test may take 5-7 business days, while a comprehensive assessment covering multiple systems, APIs, and infrastructure can take 2-3 weeks. We provide a detailed timeline during scoping and deliver preliminary critical findings within the first few days so you can begin remediation immediately.
Are pentest reports accepted for compliance audits?
Yes, our penetration testing reports are fully compliance-ready and accepted by auditors for SOC 2, ISO 27001, PCI-DSS, HIPAA, and other frameworks. Reports follow industry-standard formats, include executive summaries for leadership, technical details for engineering teams, and evidence documentation that maps directly to compliance control requirements. Our testers hold CISSP, OSCP, and CREST certifications recognized internationally.
How much does a pentest cost?
Penetration testing costs depend on scope, complexity, and the number of targets. Engagements typically start from $3,000 USD for a focused web application test. Comprehensive assessments covering multiple applications, APIs, and infrastructure range from $8,000-$20,000+. We offer transparent pricing through our pentest calculator — get an instant estimate based on your specific requirements with no hidden fees.
How is a pentest different from a vulnerability scan?
A vulnerability scan is an automated tool that identifies known vulnerabilities — it's fast but produces many false positives and cannot find business logic flaws. A penetration test is a manual, expert-led assessment where certified security professionals think like real attackers, chain vulnerabilities together, test business logic, and validate exploitability. Pentests find critical issues that scanners miss, including authentication bypasses, privilege escalation paths, and data exposure risks.
Ready to Secure Your Infrastructure?
Request a security assessment or speak with our experts